4-day training: Advanced Detection Engineering in the Enterprise
Advance your team's detection engineering skills
FalconForce developed a 4-day, instructor-led, hands-on training for security professionals. To help improve your detection engineering capabilities: Advanced Detection Engineering in the Enterprise (ADE).
We can facilitate a private training for security teams in large enterprises, or cohort-based training at global esteemed cybersecurity conferences.
Elevate your skills now, to better understand attacker behavior and optimize your detection engineering practices.
Hands-on training in your enterprise or at a conference (such as Black Hat and InsomniHack)

for cybersecurity engineers who want to build better detections
Introducing the ADE training
learn to build resilient detections
Understand attacker behavior
- Building resilient and automated detection capabilities requires a detailed understanding known or expected attacker behavior. Think like an attacker, understand the different TTPs used and what indicators can be extracted – and develop better detection capabilities.
- Our training focuses on the entire detection engineering cycle: defining a scope, researching the relevant techniques, building the detection analytic, investigating which logs can be utilized, and validating the resilience of the analytic against evasion.
- We include adjacent topics, like maintenance, testing, improvement, (response) automation and documentation.
Highly interactive training
Great learning experience
- We deliver the training in-person with two experienced facilitators. The training is highly interactive, balancing theory and a lot of hands-on exercises.
- Students get a dedicated lab environment and work on exercises through our lab guide, with the option to get hints and (partial) solutions. This allows students to get familiar with the detection engineering methodology and prepare them to start implementing this practice at their organizations.
- Students will receive reference materials, training slides, and tools and scripts used in the training.
Pricing
Private or public training
- Private training. Train your internal team(s) at a location of your choice. Benefit from more focused discussions on your organization’s specific detection engineering challenges. Great for cross-team knowledge exchange and awareness.
- Public training. Want to take the training individually or with a small group? Then join one of our public trainings at well-known security conferences, such as BlackHat, InsomniHack and NorthSec.
We help you advancing your detection engineering practices
The outline of FalconForce's ADE training
Who should take the training
- Our training is intended for medior and senior level detection engineers, threat hunters, incident responders and red teamers. The methodology will also enable anyone with a hands-on role in security to learn more to improve the security posture of a company.
- Students should be familiar with Windows endpoints, Active Directory, and Azure cloud, basic PowerShell experience is a plus. Furthermore, at least some experience with Defender XDR / Sentinel and its query language (Kusto) is required.
The training focuses on Microsoft Defender XDR and Sentinel, but concepts can be applied to other stacks as well.
What topics are covered
- Detection engineering methodology: principles, testing, maintenance, improvement, automation.
- Endpoint: Initial Access, Command and Control use and detection, Credential Dumping, Lateral Movement.
- Cloud infrastructure: Entra ID abuse and misconfigurations, Azure KeyVault and Storage Accounts, Azure Virtual Machine attacks.
- Active Directory and server-side attacks: Kerberos attacks, Active Directory Certificate Services (ADCS).
Scenario-based setup
The training covers a full, realistic attacker scenario in an enterprise environment: from the endpoint, through the Active Directory and into the cloud environment. This training is led by experienced instructors that teach students to:
- Understand how to research an attacker technique used in corporate environments.
- Build resilient detections that are harder to evade by an attacker.
- Validate their detections to make sure they keep functioning as intended.
Steps to get a private training
Discuss preferences
Get in touch and we will discuss details of the training and your preferences. For example, if certain training topics are more important to you.
Approve proposal
We will draft a proposal for the private training for your approval.
Schedule the training
Together, we decide on the timing of the training and plan our trainers accordingly.
Prepare for the training
We will prepare the training materials and lab environment. You book a location and arrange logistics for your trainees. Trainees will receive preparation materials and lab credentials before the training.
Deliver the training
Our facilitators deliver the training to your team with a combination of theory and lots of hands-on exercises. We always make room for deep-dive discussions!
After-care
After the training, we will share reference materials with the trainees. Each trainee will receive a certificate of attendance.
Training materials included
Digital lab guide
Use our digital lab guide and reference materials to perform a variety of hands-on exercises. Examples, hints and solutions are included. The lab guide includes various reference materials, such as a KQL guide. The reference materials can be downloaded for later usage as well.
Training slides
We use detailed slides to explain theory, concepts and loads of practical examples. We will provide the slides for download, so you can use them as reference for your engineering activities at your own organization.
Lab environment
You will get access to a training environment to perform exercises in a lab setup. The environment includes Windows and Linux systems with commonly used applications and settings, as well as a Microsoft Defender and Sentinel setup.
What our trainees say
“I have done many different courses over the last 10 years at Black Hat. This was by far one of the best with practical application and relevancy. The trainers provided the right depth which one would expect from an advanced course. Thanks for a great 4 days!”
Conference training participant
“I really enjoyed taking this class! I particularly enjoyed the way the labs were set up and being to work from both a red and blue team perspective. Thanks so much!””
Conference training participant
“Thanks for the great training. It was valuable, well structured, and informative. I was able to follow the training and the exercises even though I lack some knowledge, hints helped me to keep up. Hints / solutions themself can be very informative and teaching.”
Private training participant
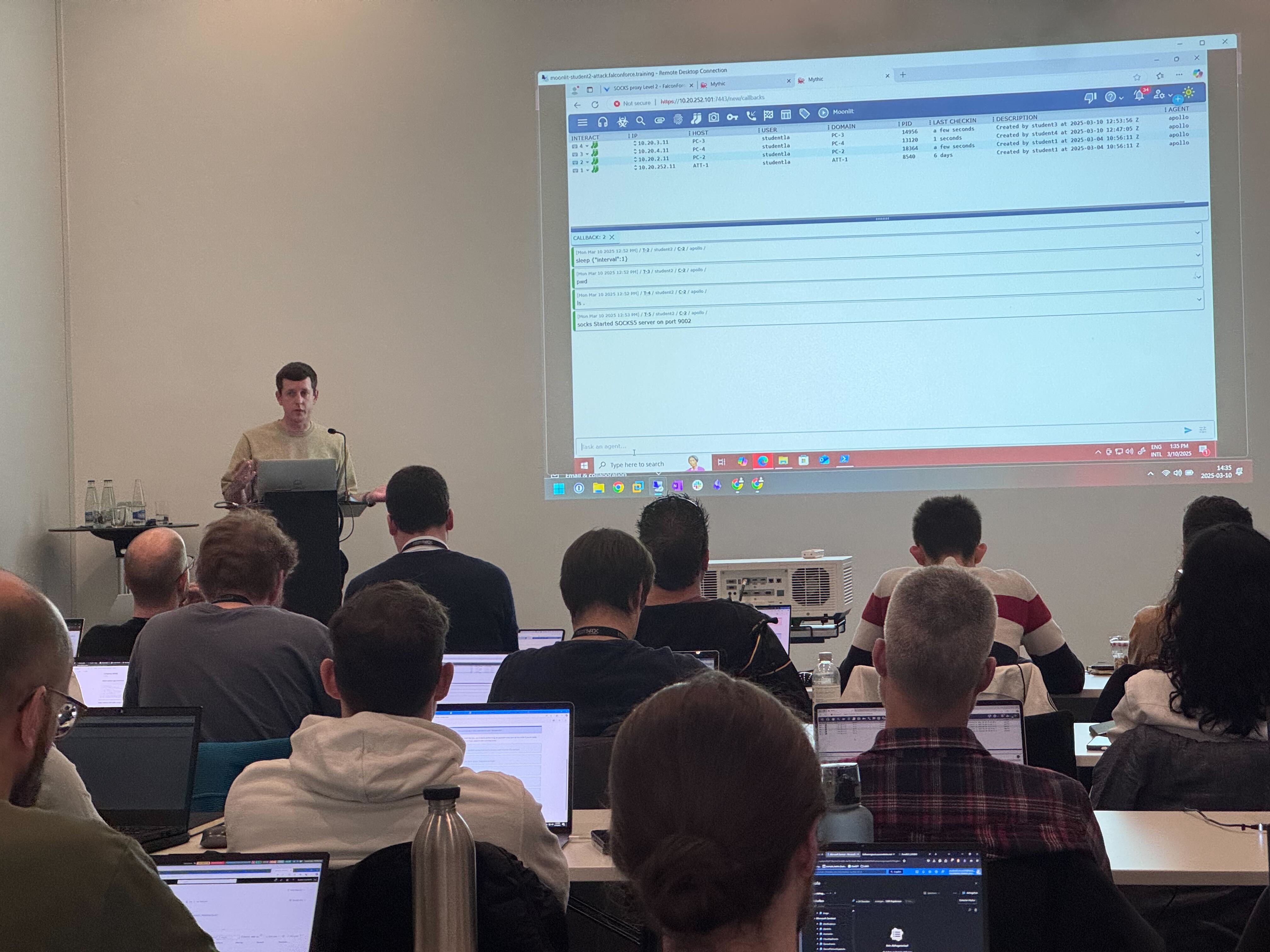
James facilitating our training at InsomniHack
We are happy to meet you and discuss how we can help. Please reach out to Givan to start a conversation!
Email: [email protected]
Phone: (+31) 85 044 93 34
Frequently asked questions
Do you provide the ADE training online?
Can you train my whole team?
Energieweg 3
3542 DZ Utrecht
The Netherlands
FalconForce B.V.
[email protected]
(+31) 85 044 93 34
KVK 76682307
BTW NL860745314B01

